The Health Insurance Portability and Accountability Act (HIPAA) is a national standard for protecting patient health information from unauthorized disclosure. Originally enacted in 1996, HIPAA has since evolved to include new policies and standards for protecting digital healthcare data exchanges:
In 2005, the HIPAA Enforcement Rule was added to address compliance issues. In 2013, the HIPAA Omnibus Rule became effective, bringing substantial updates to the original Security, Privacy, Breach Notification, and Enforcement Rules.
Later on, the compliance scope was also extended to include new entities working with Protected Health Information (PHI) and Personally Identifiable Information (PII), including medical software developers.
Today, HIPPA compliance requirements concern two groups of entities, working with PHI and PII: Covered entities and Business associates.
| Definition | Covered entities include healthcare plans, providers, and clearinghouses that exchange healthcare information electronically. |
Business associates include organizations and individuals that store, collect, process, or transmit PHI on behalf of covered entities. |
| Types of users | Doctors, nurses, researchers, etc. | Insurance companies, accountants, legal counsel, and any digital intermediaries. |
| Which healthcare software needs to be HIPPA compliant? | Any software that facilitates doctor-patient interactions: EHR/EMR systems, appointment scheduling software, patient portals, etc. | Any software that has access to protected healthcare data: cloud service providers, data analytics applications, medical software vendors, etc. |
| Which healthcare software isn’t regulated? | Any type of personal wellness product that isn’t used by medical professionals: fitness trackers, prescription reminder apps, weight loss apps, etc. | Any type of software that doesn’t interact with PHI/PII: IT infrastructure monitoring tools, threat detection systems, etc. |
In other words, HIPAA covers a wide range of prolific healthcare software products and extends to adjunct systems used in hospitals (e.g., for claims management or account reconciliation).
To tout the claim of HIPPA-compliant software, vendors must implement all the required standards and safeguards.
What is HIPAA-Compliant Software? Key Requirements
To qualify as HIPAA-compliant, software must implement several administrative, technical, and physical safeguards for protecting data.
The US Department of Health and Human Services (HHS) lists all HIPPA requirements. Here’s a summary.
HIPAA Privacy Rule
The utmost protection of patient privacy is the core HIPAA requirement. In summary, covered entities and business associates must define the limits and circumstances of when e-PHI may be used and disclosed.
There’s a limited number of permitted uses and disclosure scenarios that don’t require the patient’s authorization. These include disclosures to concerned individuals or usage of e-PHI for treatment, payment, and healthcare operations, for example. Data owners must also be provided with a clear opportunity to agree, acquiesce, or object to data usage.
For data analytics purposes, healthcare companies can use a limited data set with PII removed and/or anonymized. Such data can be used for research purposes, healthcare operations, and public health purposes.
The Privacy Rule also explicitly covers marketing activities. A covered entity must obtain authorization before using or disclosing protected health information for marketing, except for the provision of promotional gifts of nominal value and face-to-face marketing communications.
Overall, all e-PHI disclosure must be limited to the “minimum necessary” with strict authorization measures in place.
HIPAA Security Rule
Data security is the cornerstone HIPPA requirement. To comply, organizations, their business partners and healthcare software providers must:
- Ensure unquestionable confidentiality, integrity, and availability of all e-PHI
- Implement proper security mechanisms for information protection
- Ensure that no impermissible uses or disclosures will occur
- Certify compliance with the Security Rule by their workforce
In practice, this translates to several provisions concerning how data is stored, managed, and exchanged.
Security Rule confidentiality requirements complement Privacy Rule prohibitions against improper use and disclosure of PHI. The “integrity” clause means that e-PHI must not be altered or destroyed in an unauthorized way, while "availability", on the contrary, indicates accessibility to authorized users.
The Security Rule doesn’t give hard guidelines on how all of the requirements have to be achieved but rather provides “broad stroke” recommendations. Each organization can select the optimal approach to compliance by factoring in:
- Its size and capabilities
- Existing technical infrastructure
- The costs of different security solutions
- Risk exposure of e-PHI
In other words, you can take different approaches to HIPAA-compliant software development.
Administrative Safeguards
Administrative Safeguards mainly concern organizational processes healthcare institutions have in place to ensure compliance with the HIPAA Security Rule. The measures include proper security management processes, sufficient workforce training, effective information access management, and availability of sufficient security personnel. These requirements don’t directly concern medical software vendors.
Physical Safeguards
Physical safeguards also only concern covered entities, which must ensure appropriate facility access controls (to prevent physical unauthorized entry) and robust protection of the workstations and devices. Specifically, healthcare institutions must design appropriate policies for the transfer, removal, disposal, and re-use of electronic media to protect e-PHI.
Organizational Requirements
Both the covered entities and their business associates are bound to provide timely disclosures of material breaches or violations in e-PHI usage. Failure to do so can result in substantial fines and ongoing regulatory investigations.
This requirement is also known as the Breach Notification Rule.
Policies and Procedures and Documentation Requirements
Covered entities must implement appropriate organizational policies to comply with the Security Rule and maintain written records of these. When environmental or organizational changes affect the security of electronic protected health information (e-PHI), covered entities must review and update their documentation.
Technical Safeguards
Technical safeguards include specific standards for HIPAA-compliant software development, so this section concerns vendors the most.
Specifically, healthcare software providers must ensure that their product includes:
- Sufficient technical policies and procedures for access control management.
- Appropriate hardware, software, and/or procedural mechanisms to provide easy auditability of the system.
- Mechanisms and policies to prevent unauthorized alteration or deletion of e-PHI.
- Security measures that prevent unauthorized access to e-PHI transmissions.
We’ll go over each one of these in the next section.
Risk Analysis and Management
Finally, as part of the HIPAA Security Rule, covered entities and business associates need to perform ongoing risk analysis.
Risk analysis should include the following activities:
- Regular evaluations of the likelihood and impact of potential risks to healthcare data.
- Timely implementation of protective measures to address the newly identified risks.
- Proper documentation of the implemented security measures
- Implementation of continuous, reasonable, and appropriate security protections
HHS offers a handy Security Risk Assessment Tool organizations can use for risk analysis. And the NIST HIPAA Security Toolkit Application can guide the selection of proper security measures.
How to Make HIPAA Compliant Software: Best Practices + Checklist
To launch a HIPPA-compliant product, software vendors must implement all the recommended Technical Safeguards — a set of standards for ensuring data security. HHS doesn’t push for the usage of specific security tools (e.g., AWS Security Tools) or security models (e.g., Zero-Trust security models). Likewise, the HIPAA Security rule doesn’t prohibit the use of public cloud services, as long as the solutions comply with the broader rules (e.g., Amazon HealthLake).
The Security Rule is based on the fundamental concepts of flexibility, scalability, and technology neutrality. Therefore, no specific requirements for types of technology to implement are identified.
The intentional technology agnosticism gives more room for maneuvers. But it also often creates confusion around how to make software HIPAA-compliant and what architecture patterns to best use.
Svitla Systems has successfully delivered several HIPAA-compliant products, including a hospital admissions platform, genomics analysis app, and transplantation management solution, among other projects.
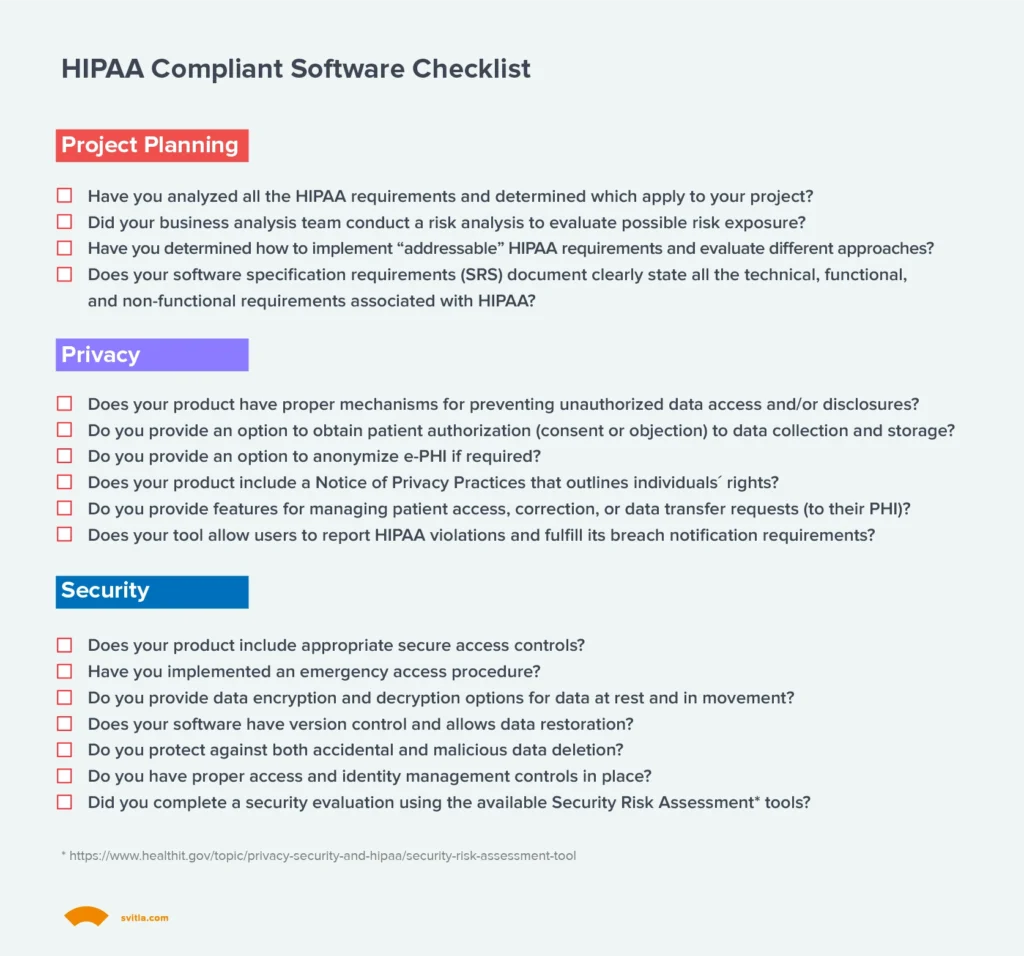
Based on our experience and analysis of NIST and HHS recommendations, we’ve created a HIPAA-compliant software checklist we rely on when deciding on the optimal product architecture and security controls.
1. Determine Which Rules Apply to Your Company
HIPAA concerns all organizations and individuals accessing or handling personal patient data (e-PHI). However, the compliance requirements differ slightly for covered entities and business associates.
Respectively, you may be subject to different Privacy Rule or Security Rule requirements depending on the type of software you’re building. For example, HIPAA requirements for healthcare management platforms will be more complex than those of an account reconciliation app used for insurance claims processing.
Also, some of the HIPAA standards are “required,” and others are “addressable.” Required standards mandate the implementation of specific procedures and policies. Addressable specification means you must first perform a risk assessment (e.g., with an OCR Security Risk Assessment Tool) and then take risk mitigation steps.
An experienced healthcare software development partner can guide you through applicable provisions and standards.
2. Design Secure Access Controls
The Access Control standard requires healthcare software providers to:
“Implement technical policies and procedures for electronic information systems that maintain electronically protected health information to allow access only to those persons or software programs that have been granted access rights as specified in § 164.308(a)(4)[Information Access Management].”
The rule doesn’t dictate the usage of specific identity and access management (IAM) tools or access management methods (e.g., two-factor authentication).
Yet, there are several required and recommended specifications you must implement as part of this standard:
- Unique User Identification (Required). Each user, regarding their status in the system, must have a unique ID, associated with their account. So that you could oversee the activity of specific users for audit and compliance purposes and hold them accountable for performed actions.
- Emergency Access Procedure (Required). The software must contain separate policies and procedures for access in emergencies. These can be different from standard usage protocols. The product users must be able to program which users need emergency access and under what conditions.
- Automatic Logoff (Addressable). Automatic logoff after a period of inactivity is recommended to strengthen privacy and security.
- Encryption and Decryption (Addressable). An option to encrypt/decrypt electronic health information should be made available. The standard doesn’t mandate the usage of specific data encryption protocols but leaves this decision to the software developer. End-users from the covered entities can then decide on which e-PHI should be encrypted.
In each case, you’re allowed to select the most appropriate approach for implementation.
3. Implement Property Data Protection Mechanisms
The next primary requirement for HIPAA-compliant software is high data integrity. e-PHI must be protected against unauthorized, accidental, or intentional alteration or destruction. This standard designates how e-PHI must be protected against any potential compromises. The official standard doesn’t further elaborate on the exact measures.
Sample strategies for ensuring data integrity according to HIPAA can include:
- Appropriate IAM controls, preventing data removal by low-level users
- Regular data backups and automatic restores
- Clear data lineage and version control
- Effective data governance practices
Effectively, you must ensure that no e-PHI entering your software would be altered or destroyed unauthorizedly.
4. Implement Proper Access and Identity Management Controls
Access to protected health data must be properly authenticated. Again, you’re free to select the best-suited measures:
- Usage of passwords or PINs
- Two-factor authentication
- Biometric authentication
Or any combination of the above methods.
Your system must also have a clear structure of access privileges, which allows for limiting the users’ interaction with e-PHI. For example, only users with the highest account privileges can modify the data.
5. Secure data in movement
Secure transmission (exchanges) of e-PHI is one of the central HIPAA software requirements. Whether e-PHI is shared between two on-premises systems, uploaded to cloud storage, or transmitted to a business associate (e.g., an insurance company), it must be properly protected.
You have two recommended implementation specifications:
- Integrity Controls (Addressable). Software vendors must ensure full integrity of transmitted data (i.e., protect it from accidental or malicious alterations) during transmission. In practice, this means using secure web communication protocols like https, for example.
- Encryption (Addressable). When appropriate e-PHI, should be also encrypted during transmission. Again, you have free reign on the implementation approach.
6. Develop with Auditability in Mind
Last but not least comes the Audit Controls standard:
“Implement hardware, software, and/or procedural mechanisms that record and examine activity in information systems that contain or use electronic protected health information.”
HIPAA-compliant software must be easily auditable, providing users with controls to extract and examine the system activity when needed. Software auditability promotes easier reporting on compliance and helps provide clear-cut evidence of whether a violation took place.
Download HIPAA Compliant Software Checklist
Get a free checklist from our team:
Conclusions
At first glance, HIPAA-compliant software requirements may appear highly complex. But in practice, most of the HIPAA standards closely match the more general software development best practices: Strong focus on data privacy, appropriate authentication and system usage methods, and secure data storage and exchanges.
And because there’s no one-size-fits-all HIPAA compliance checklist, healthcare vendors can take advantage of the latest innovations in security technology: Zero-trust security, passwordless authentication, behavioral security analytics, etc., to create both user-friendly and compliant digital healthcare solutions.
If you have any further questions about HIPAA-compliant software development, reach out to Svitla Systems. We’d be delighted to walk you through different standards and help with risk evaluations and digital product development.





